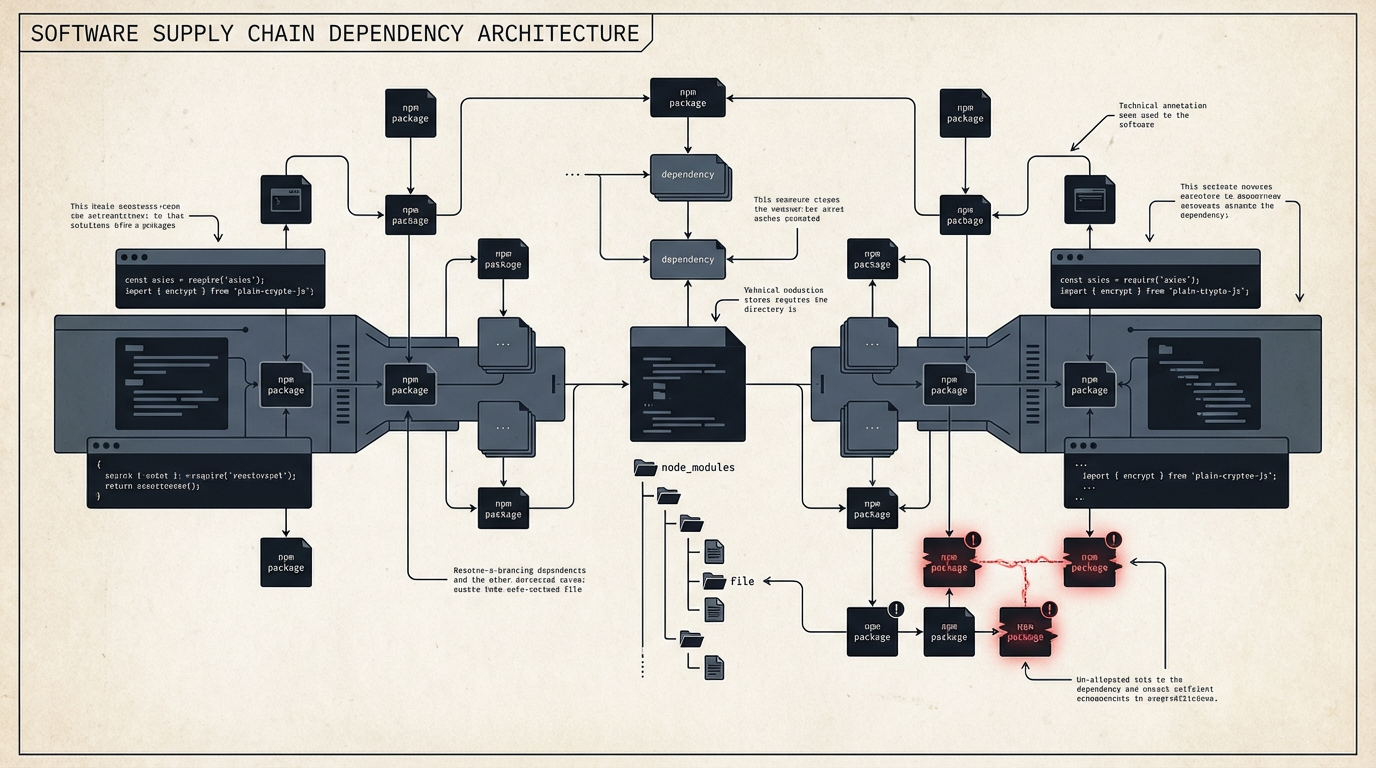
NEW YORK — Suspected North Korean hackers hijacked the official Axios library on the npm registry on Tuesday, injecting malicious code into two new versions of the popular tool downloaded 100 million times weekly. Researchers from TechCrunch, Help Net Security, The Register, The Hacker News, Snyk, and Socket identified the breach as a sophisticated supply chain attack targeting macOS, Windows, and Linux environments. Each of the bullet points immediately below have been confirmed by at least four of the six respected sources we curated on this story.
- Attackers published malicious versions axios@1.14.1 and axios@0.30.4 to the npm registry on Tuesday.
- The compromise was achieved by hijacking the npm account of Axios’s primary maintainer, Jason Saayman.
- The malicious payload was delivered via a rogue dependency named plain-crypto-js@4.2.1, which was pre-staged 18 hours in advance.
- Google’s Threat Intelligence Group (GTIG) attributed the campaign to a suspected North Korean threat actor tracked as UNC1069.
- The malware automatically executes a post-install script that deploys remote access trojans (RATs) tailored to the victim’s operating system.
- After execution, the malware erases its own binaries and swaps the package manifest with a clean “decoy” to hide its tracks.
- Analysts confirmed this incident is unrelated to the recent series of supply chain attacks attributed to the group TeamPCP.
Additional Details Reported
The malicious Axios versions were live on the npm registry for nearly three hours on Tuesday before they were yanked by the registry’s security team. Security firm StepSecurity reported that the attackers locked the project’s lead maintainer out of his account by changing the registered email address to a ProtonMail inbox (ifstap@proton.me). This allowed the hackers to bypass traditional GitHub Actions CI/CD pipelines and publish directly via the npm command-line interface.
The malware uses a two-stage dropper mechanism. The first stage identifies the host platform and contacts a command-and-control (C2) server at 142.11.206.73 or sfrclak.com:8000. On macOS, the malware disguises itself as a system daemon at /Library/Caches/com.apple.act.mond. Windows systems are infected via a PowerShell script masquerading as the Windows Terminal app at %PROGRAMDATA%\wt.exe, while Linux victims receive a Python script at /tmp/ld.py.
The remote access trojan (RAT) beaconing interval is set to 60 seconds, allowing attackers to maintain persistent control and execute arbitrary shell commands or additional binaries. Technical analysis by Elastic Security Labs revealed significant code overlap between the macOS binary and a backdoor known as WAVESHAPER, which was previously linked to North Korean state-sponsored operations.
Supply chain security company Socket also identified two additional packages, @shadanai/openclaw and @qqbrowser/openclaw-qbot, which were found to be distributing the same malicious dependency. Developers who installed the affected versions are urged to isolate their systems, rotate all credentials—including API keys and SSH secrets—and rebuild their environments from known-clean snapshots.
How we report: We select the day’s most important stories, confirm facts across multiple reputable sources, and avoid anonymous sourcing. Our goal is clear, balanced coverage you can trust—because transparency and verification matter for informed readers.
Image Attribution ▾
Attribution: AI-generated image (Hedra.com for EOBS.biz)
License: CC-BY-NC-SA 4.0 via Hedra.com
Source: https://api.hedra.com
Modifications: None
Prompt: deliverables/news-image-2026-03-31-hedra-prompt.txt
Decision: projects/news/outputs/news-image-2026-03-31-technology-visual-selection.txt